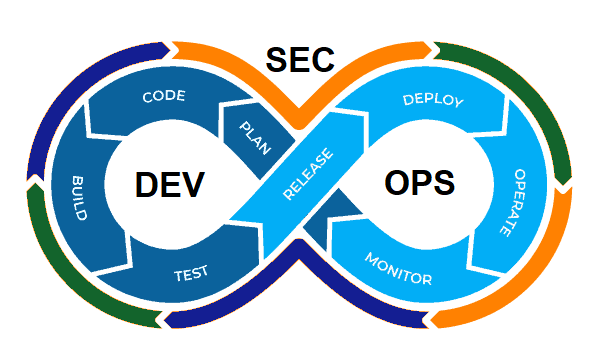
From DevOps to DevSecOps
DevSecOps (Development, Security & Operations) is a transformational shift in the digitally evolving IT world which incorporates secure culture, practices, and tools to drive visibility, collaboration, and agility of security into each phase of the DevOps pipeline.
Why DevSecOps is crucial for your business:
- Continuous Security- DevSecOps uses automated security review of code and automated application security testing.
- Increased efficiency & quality: Security issues are detected and remediated during development phases which increases the speed of delivery and enhances quality.
- Enhanced compliance: In DevSecOps, security auditing, monitoring, and notification systems are automated and continuously monitored, which facilitates enhanced compliance.
- Increased collaboration: By integrating development, security and operations, DevSecOps fosters a culture of openness and transparency from the earliest stages of development.
SNP’s Approach to DevSecOps:
SNP Technologies, leverages Microsoft Azure to implement a DevSecOps framework that focuses on services like:
- Vulnerability assessment and threat investigation.
- Automated code analysis and review.
- Secure releases of CI/CD pipeline.
- Huge cost savings.
- Scalability and improved resilience by deploying microservices and containers.
- Automated security and monitoring for enhanced compliance.
DevSecOps Implementation:
Infrastructure Security
- This is an access control and centralized authentication mechanism.
- Role-based Access Control (RBAC) is required for secure access to clusters and namespaces with identity managed at the container level to grant secure access to specific Azure resources.
- Ingress controllers can be used to define internal IP addresses, so services are accessible internally.
- Network isolation can play a key role as network policies are used to manage pod-to-pod communications or from an IP outside of the cluster.
- Data is encrypted between apps and services; this includes both data in transit and data at rest.
Container/Pod Security
- Pod managed identities are leveraged to secure and authenticate images and other resources in the container registry.
- Credentials are requested and retrieved from digital vault/key vault.
- Isolation is done at pod level security policies which enables fine-grained authorization to pods using pod security to limit access and services.
Security Management
- Manual errors are eliminated by integrating security scanners, running security static analysis tools and scanning any pre-built container images in the build pipeline.
- Security events on the cluster are monitored for attacks with log analytics integration.
Why SNP?
At SNP, we help you choose and implement a right DevSecOps solution which aligns with your technology roadmap. For more information, contact us here.